Introduction
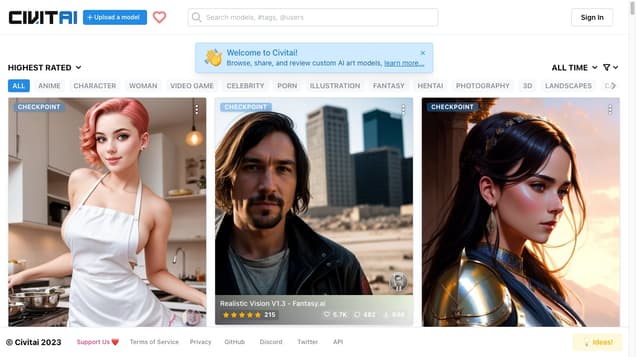
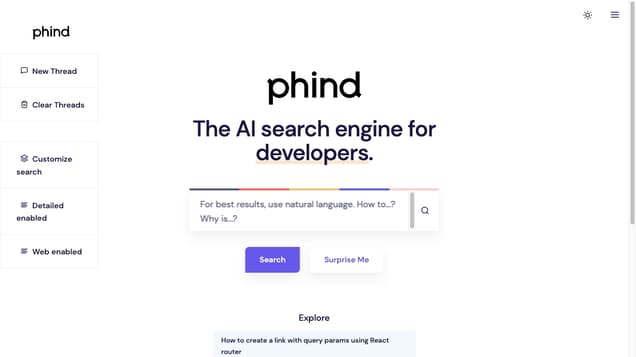
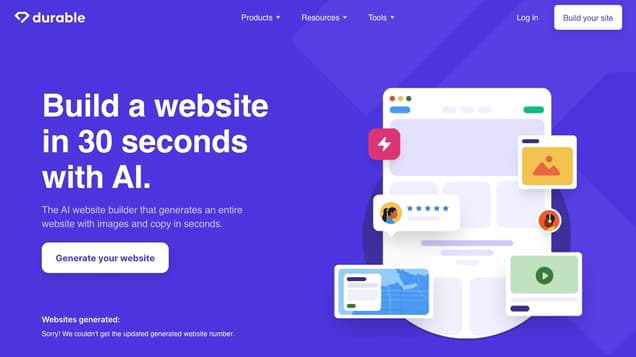
Welcome to Freework.AI, your ultimate destination for exploring the world of artificial intelligence tools. In an era where AI is reshaping every aspect of our lives, Freework.AI emerges as a comprehensive directory, dedicated to connecting users with a diverse range of AI tools. Whether you're an E-Commerce Owner, Influencer, Indie Hacker, or Designer, our platform is tailored to meet your unique AI tools needs, helping to streamline your work and enhance productivity.